CryptoDB
Secure Quantum Computation with Classical Communication
| Authors: | |
|---|---|
| Download: | |
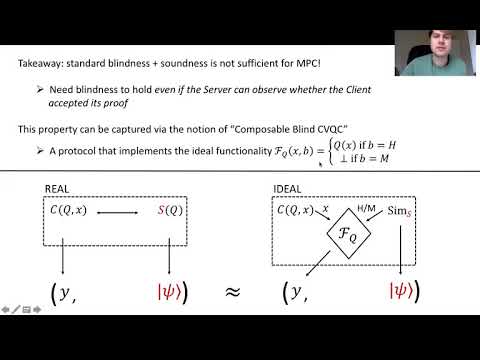
| Abstract: | The study of secure multi-party computation (MPC) has thus far been limited to the following two settings: every party is fully classical, or every party has quantum capabilities. This paper studies a notion of MPC that allows some classical and some quantum parties to securely compute a quantum functionality over their joint private inputs. In particular, we construct constant-round \emph{composable} protocols for blind and verifiable classical delegation of quantum computation, and give applications to secure quantum computation with classical communication. Assuming QLWE (the quantum hardness of learning with errors), we obtain the following (maliciously-secure) protocols for computing any BQP (bounded-error quantum polynomial-time) functionality. - A six-round protocol between one quantum server and multiple classical clients in the CRS (common random string) model. - A three-round protocol between one quantum server and multiple classical clients in the PKI (public-key infrastructure) + QRO (quantum random oracle) model. - A two-message protocol between quantum sender and classical receiver (a quantum non-interactive secure computation protocol), in the QRO model. To enable composability of classical verification of quantum computation, we require the notion of \emph{malicious blindness}, which stipulates that the prover does not learn anything about the verifier's delegated computation, even if it is able to observe whether or not the verifier accepted the proof. To construct a protocol with malicious blindness, we use a classical verification protocol for sampBQP computation (Chung et al., Arxiv 2020), which in general has inverse polynomial soundness error, to prove honest evaluation of QFHE (quantum fully-homomorphic encryption) ciphertexts with negligible soundness error. Obtaining a constant-round protocol requires a strong parallel repetition theorem for classical verification of quantum computation, which we show following the "nearly orthogonal projector" proof strategy (Alagic et al., TCC 2020). |
Video from TCC 2021
BibTeX
@article{tcc-2021-31510,
title={Secure Quantum Computation with Classical Communication},
booktitle={Theory of Cryptography;19th International Conference},
publisher={Springer},
doi={10.1007/978-3-030-90459-3_1},
author={James Bartusek},
year=2021
}